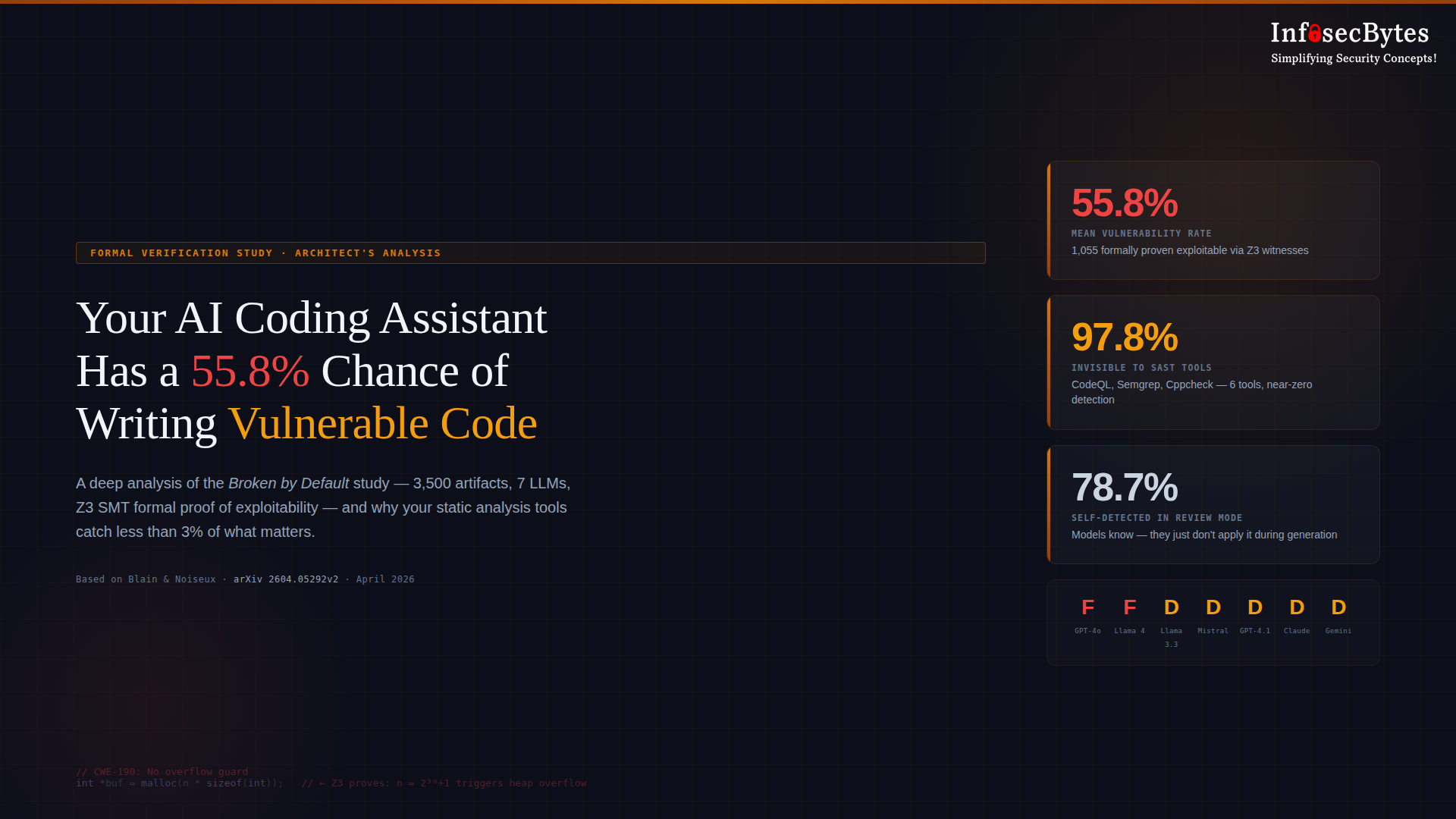
A new formal verification study — Broken by Default — used the Z3 SMT solver to mathematically prove that 55.8% of AI-generated code contains exploitable vulnerabilities. Across 3,500 artifacts from seven production LLMs, 1,055 findings were formally proven with concrete exploit inputs. The worst part? Six industry-standard static analysis tools combined — including CodeQL — missed 97.8% of them. This is a security architect’s deep analysis of what the study found, why it matters, and what security leaders need to do about it now.
The LiteLLM Supply Chain Attack: What Every AI Builder Needs to Know
On March 24, 2026, two malicious versions of LiteLLM — the Python library powering 95 million monthly downloads across the AI developer ecosystem — were quietly pushed to PyPI. The attack didn’t begin with LiteLLM. It began with Trivy, a vulnerability scanner running inside LiteLLM’s own CI pipeline without version pinning. One compromised dependency handed attackers the PyPI publishing credentials they needed. What followed was a multi-stage credential stealer that executed silently on every Python process, swept SSH keys, cloud credentials, Kubernetes tokens, and API keys, then exfiltrated everything encrypted to an attacker-controlled server. The TeamPCP campaign is still active. This is the blueprint for AI supply chain attacks going forward — and your current defenses are probably not sufficient.
Beyond the Checkbox: Why Better Compliance Doesn’t Mean Better Security
You’ve got the badges, the certificates, the shiny SOC 2 logo. 🎖️
Auditors love you. The board’s thrilled. But here’s the twist — hackers don’t care about your checklists.
Compliance proves your controls exist; security proves they work when tested.
This post isn’t another framework lecture — it’s a reality check on why “audit-ready” ≠ “breach-ready,” and how smart teams are moving from checkbox compliance to real resilience. ☕🔐🔥