Modern processor architectures are the essential elements of today’s computing that drives everything from handheld […]
LSMs & KSPP Explained: Advanced Security Strategies for Linux
Linux operating system is widely used in servers, embedded systems, cloud infrastructure and containerised environments. […]
Protecting the Core: Advanced Kernel Hardening for Secure Systems
An Operating System kernel is the heart of computer that controls how software interacts with […]
mTLS Deep Dive: Strengthening Security with Mutual TLS Authentication
In today’s cybersecurity landscape, securing communications over the internet is more crucial than ever. Transport […]
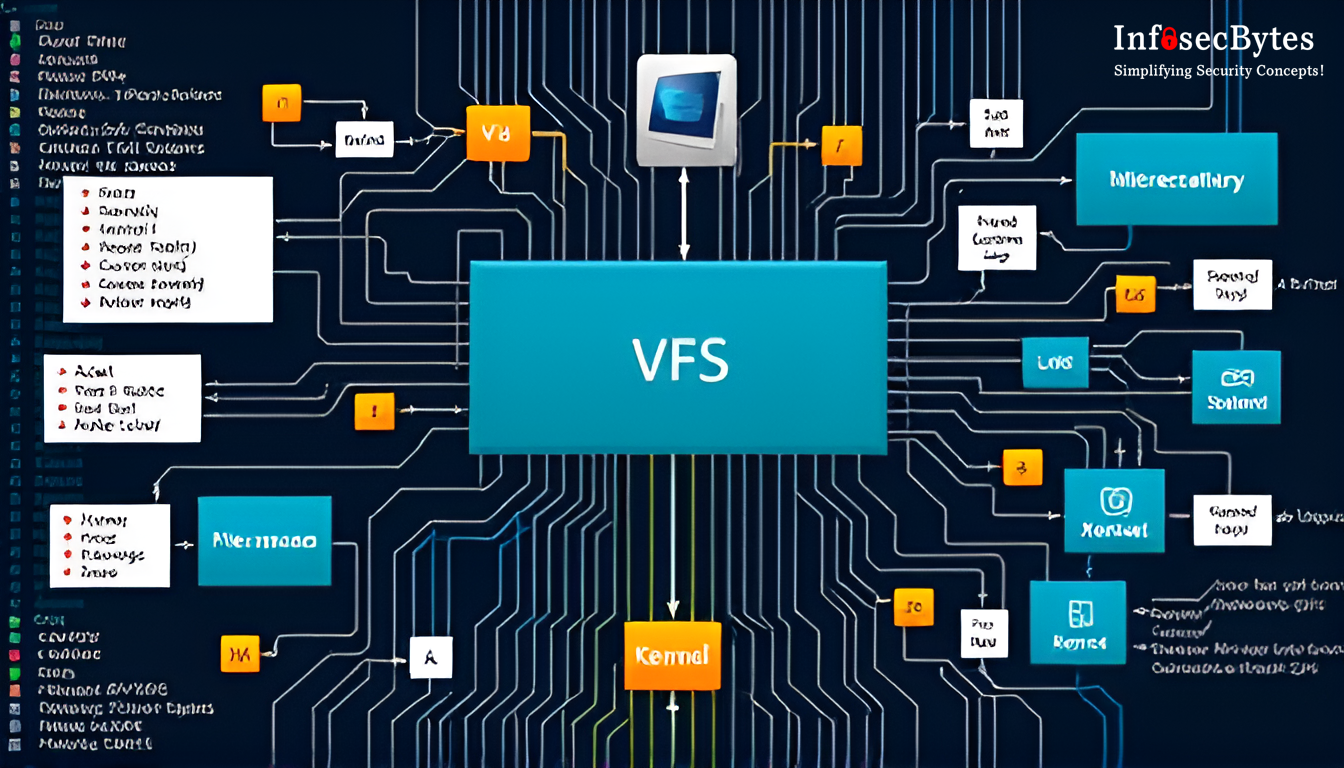
Linux Internals: Virtual File System
Imagine walking into a grand library where countless books are organized across different sections, languages, […]
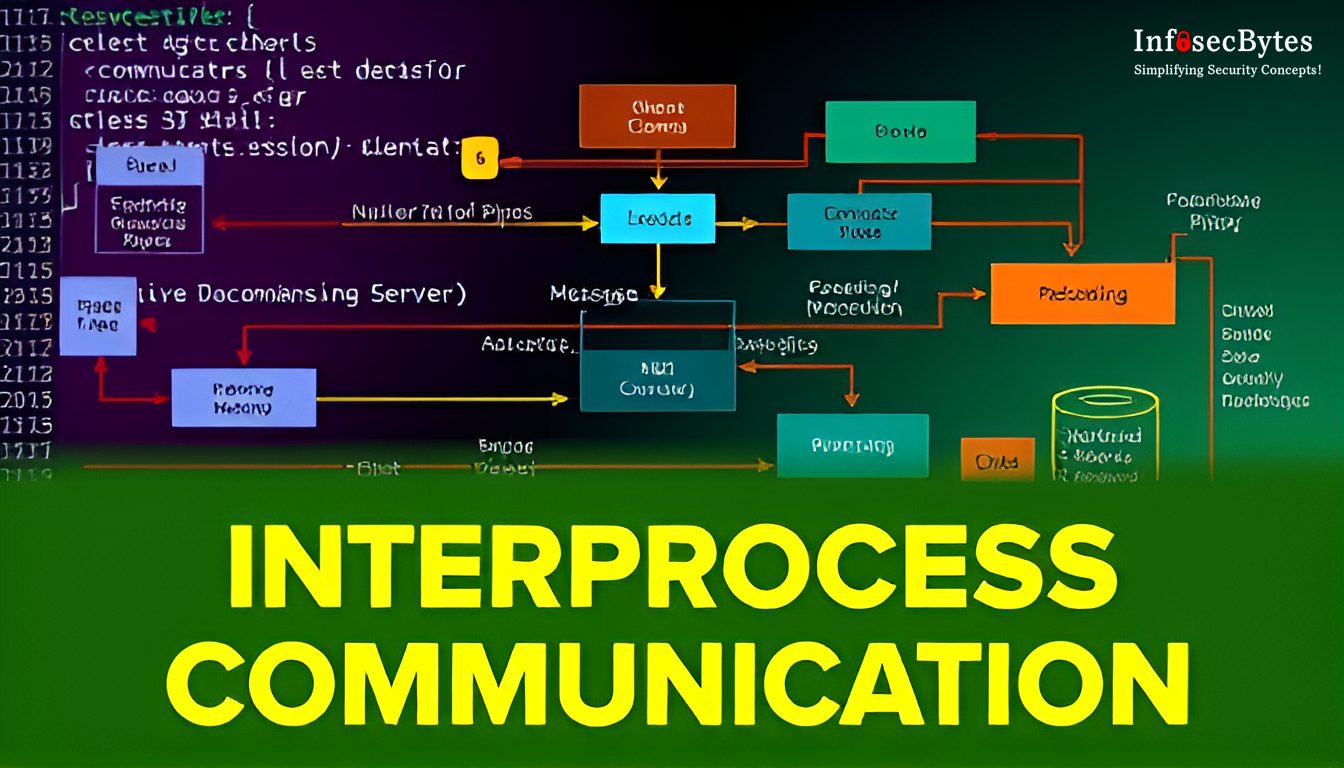
Linux Internals: Interprocess Communication
In the realm of operating systems, interprocess communication (IPC) is vital for allowing processes to […]
Linux Internals: Memory Management Explained
Memory management is a crucial aspect of any operating system, responsible for efficiently handling memory […]
Linux Internals: Process Management
Process management is one of the most fundamental aspects of an operating system. In Linux, […]
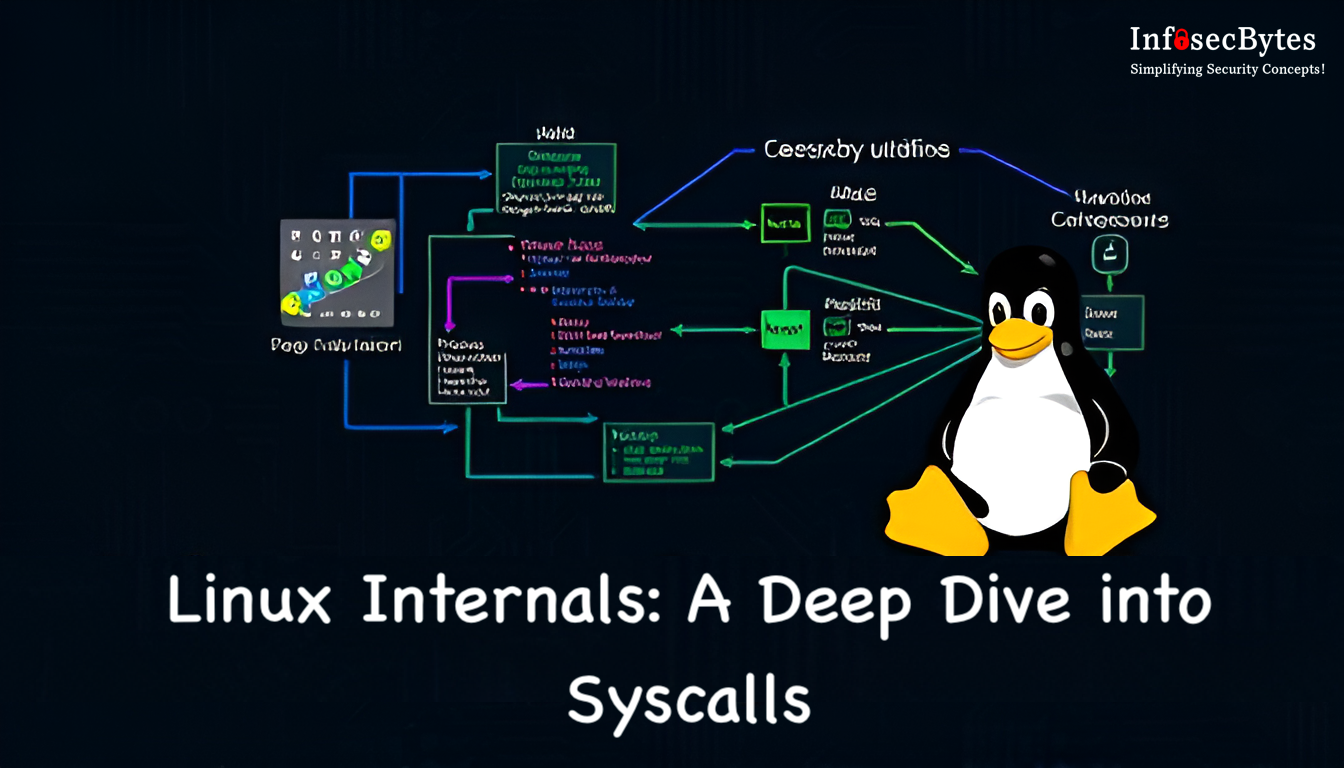
Linux Internals: A Deep Dive into Syscalls
System calls, commonly referred to as syscalls, are the backbone of communication between user space […]
Linux Internals: Understanding the Kernel Architecture
The Linux kernel is the heart of the Linux operating system, serving as the critical […]