As the technology advances, cyber threats are becoming more sophisticated and powerful than ever. In […]
ASLR Explained: Why Randomizing Memory Layouts Matters for Security
Address Space Layout Randomization, or ASLR for short, is one of the most important computer […]
Modern Processor Architectures: How Instruction Sets Drive Innovation
Modern processor architectures are the essential elements of today’s computing that drives everything from handheld […]
LSMs & KSPP Explained: Advanced Security Strategies for Linux
Linux operating system is widely used in servers, embedded systems, cloud infrastructure and containerised environments. […]
Protecting the Core: Advanced Kernel Hardening for Secure Systems
An Operating System kernel is the heart of computer that controls how software interacts with […]
Understanding SSH: History, Implementation, and Security Considerations
Secure Shell (SSH) is one of the most fundamental tools in the realm of network […]
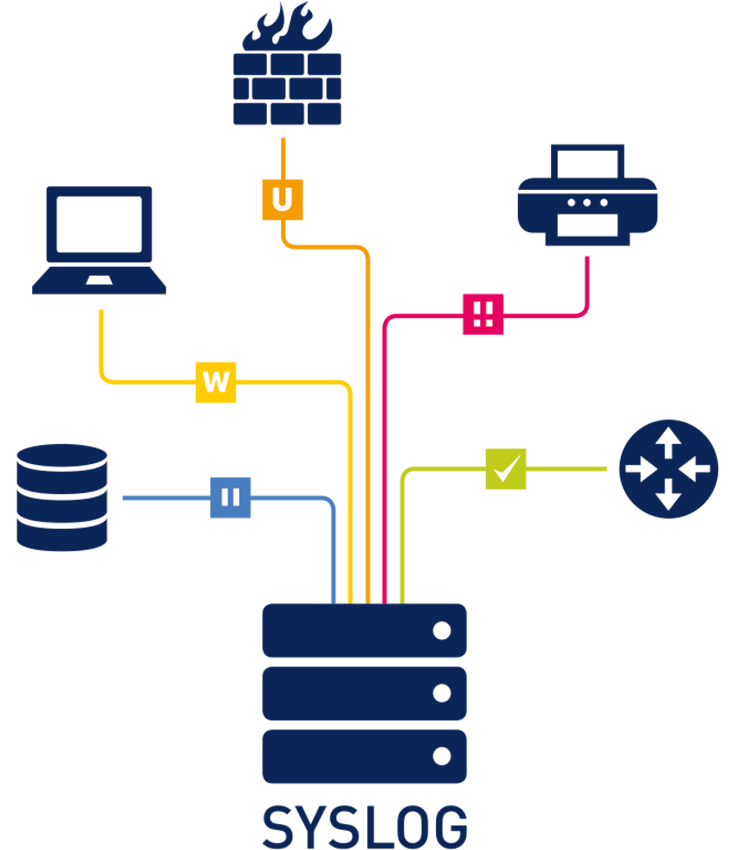
Syslog Simplified: Unveiling the Core of Logging and Monitoring
In today’s complex IT environments, managing and monitoring system events across a wide range of […]